Next-generation firewalls
TOPRSEN® Firewall adopts a multi-core pure hardware architecture and integrated software design, integrating firewall, VPN, content filtering, Internet behavior management, IPv6/IPv4 dual protocol stack, Anti-Denial of Service Attack (Anti-DoS) and other security technologies, fully supporting QoS, high availability (HA), log auditing and other functions, high performance, green and low carbon. Multi-core pure hardware architecture and integrated software design.
Intrusion detection system
Identify spam events based on the user's security posture and frequency, and optimize the policy. Analyze and deal with threats with a de-technical wizard. Reduce the maintenance workload of users; It can correlate and analyze reported events, identify important alarms, and remind users to pay attention. It can accurately and efficiently detect common network threats, abnormal traffic, and other attack behaviors. Intelligent threat analysis and comprehensive threat detection.
Zero Trust security model
Forrester Research's Zero Trust information security model is built on the foundation of threats that are everywhere, both inside and outside the enterprise. To close the gap between security and vulnerability, a multi-layered security approach is essential to optimize prevention, detection, and response. New business plans and processes add the potential for attacks, and the defense of the enterprise perimeter is no longer relevant. Applications, users, and devices are expanding outward, leaving the once-trusted enterprise perimeter defense in name only. Now, protection is needed where applications, data, users, and devices are. To close the gap between security and vulnerability, a multi-layered security approach is essential to optimize prevention, detection, and response.
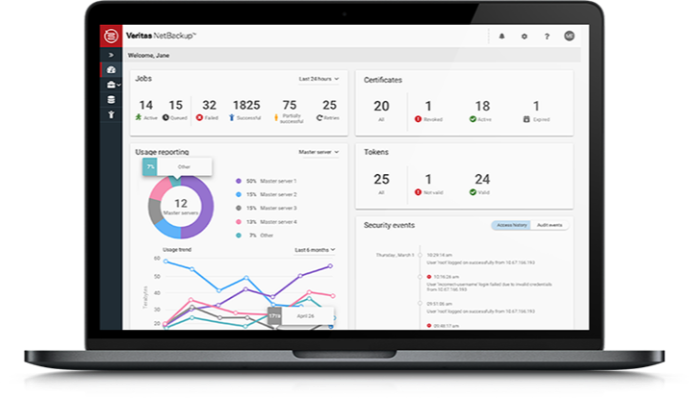
Monitoring and management platform
In just 10 minutes, we can deploy the Toprsen Monitoring Manager System in your key locations and provide comprehensive IT system health reports. The integration of network security products distributed in various places and the center TOPRSEN TMMS becomes a perfect and reliable distributed network monitoring solution, and the monitored network security products support the current mainstream brands in the industry. The distributed IT integrated management model provides enterprises with an ideal low-cost and effective management solution.
IPSEC VPN Security Gateway
A professional secure interconnection access product integrating IPSEC/SSL VPN two-in-one, Internet behavior management, firewall, and traffic control management. It is suitable for remote data interconnection of enterprises of all sizes, mobile office remote VPN access applications. The intelligent VPN management platform supports flexible and full-dynamic IP automatic VPN networking.
IT service outsourcing
The contradiction between supply and demand of talents in the software industry and the contradiction between time and space make software enterprises have cyclical demand for software development talents at different levels. SoftTrust IT service outsourcing and software talent dispatch belong to Liaoning SoftTrust Information Technology Co., Ltd., which is committed to independent product innovation and solves the problem of software project talent shortage, providing professional software talent services for software enterprises. It is one of the few talent service agencies in China with an independent software talent database. SoftTrust is a perennial talent service provider for well-known domestic and foreign companies such as VMware, Leybold, and Neusoft. At present, SoftCredit has set up branches in major software cities in China, realizing the strategic deployment of "based on the northeast and serving the whole country". Provide manpower guarantee for cross-regional project implementation of software enterprises.