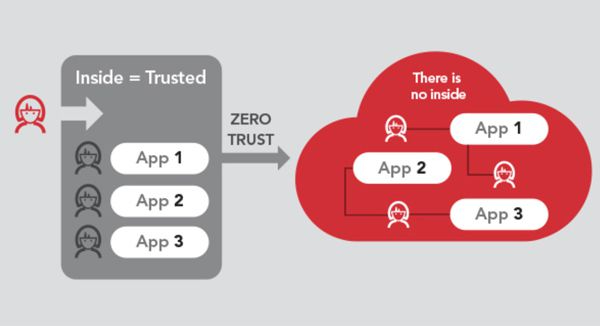
Why do you need a Zero Trust security model?
To close the gap between security and vulnerability, a multi-layered security approach is essential to optimize prevention, detection, and response.
Forrester Research's Zero Trust information security model is built on the foundation of threats that are everywhere, both inside and outside the enterprise. To close the gap between security and vulnerability, a multi-layered security approach is essential to optimize prevention, detection, and response. New business plans and processes add the potential for attacks, and the defense of the enterprise perimeter is no longer relevant. Applications, users, and devices are expanding outward, leaving the once-trusted enterprise perimeter defense in name only. Now, protection is needed where applications, data, users, and devices are.
Users, devices, applications, and data are moving beyond the enterprise perimeter and control area.
New business processes driven by digital transformation increase risk.
The "trust, but also validate" philosophy no longer applies as advanced targeted threats are moving within the corporate perimeter.
Traditional border defenses are not only complex, but also increase risk and no longer fit into today's business models.
Zero Trust Data
Traditional Perimeters Are Dead: Microboundaries Are Forever
In the cloud age, data is at the heart of security architecture. We don't have to rely entirely on firewalls because your sensitive data is no longer always within a secure perimeter, but is being transferred back and forth between on-premises and in the cloud.
In a zero trust model, you can't trust anything in and out of the network: creating a new, data-centric perimeter around information and protecting data with strong authentication techniques associated with intelligent authentication is the best security solution. Blindly allowing users access to data without checking their identity can kill the entire security stack.
Zero Trust implementations rely on protections that provide as much insight into the specific users who access data, whether it's on-premises or in the cloud. Only when all the risk factors around the user and their authentication device are they assessed can the data be truly clear.
In short: protect your data and don't trust anyone. Our Zero Trust data solutions include:
-
Data Loss PreventionInformation Centric Security (ICS)
-
Encryption
-
Validation and ID Protection
-
Information Centric Tagging
-
Information Centric Analytics

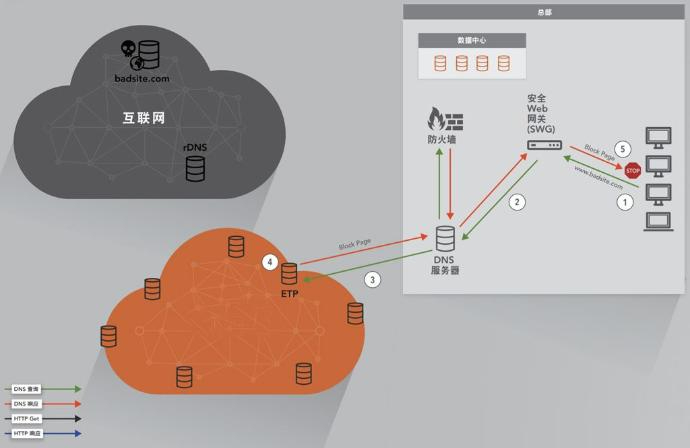
Zero Trust Networking
Divide, isolate, and control your network
Implementing a zero trust model requires strong network control capabilities that can divide and isolate data and resources. Modern networks are a mix of on-premises, web-based, and cloud-based systems that require seamless protection wherever data flows.
Zero Trust workload solutions include:
-
Cloud Workload Protection
-
Web Application Firewall
-
Cloud Access Security Broker
-
Control Compliance Suite
-
Symantec Protection Engine
Visibility and analytics
In the Zero Trust space, visibility is critical
Threats are everywhere, and attackers use increasingly sophisticated tactics, such as hiding in encrypted communications to evade detection. Visibility technology protects against their attacks and helps detect and respond to risks in a timely manner.
Zero Trust technologies include:
-
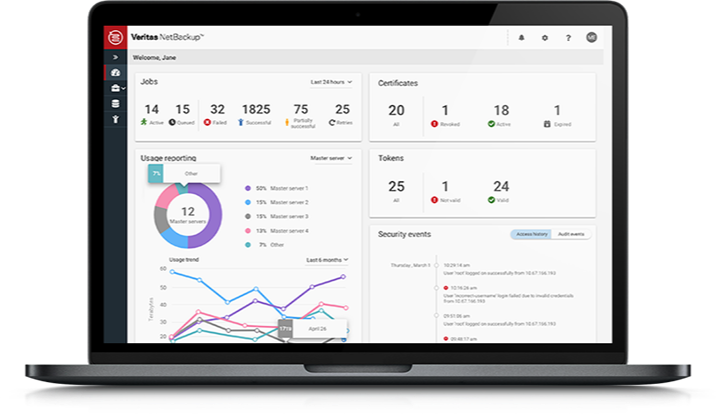
Security Analytics
-
Encrypted Traffic Management
-
Information Centric Analytics
-
Call Center Security
-
Endpoint Detection and Response
-
Cloud Access Security Broker
Zero Trust workloads
Protect your entire application stack with our integrated technologies
Apply Zero Trust workload principles to protect the front-end and back-end systems that support daily business operations. Whether on-premises or in the cloud, these connections, applications, and components are weak threat entry channels.
Remember: if you run your workloads in the public cloud, your data is stored on someone else's computer.
-
Cloud Workload Protection
-
Web Application Firewall
-
Cloud Access Security Broker
-
Control Compliance Suite
-
Symantec Protection Engine
Zero Trust automation and orchestration
Integrated solutions enable effective command and control
When choosing a strategic partner with leading technology, it's important to prioritize simplicity and efficiency, which can only be achieved through integration, automation, and orchestration. This is Symantec's overall strategy. We call this an integrated cyber defense platform (ICD). We are committed to building an extensive network of trusted cybersecurity partners through the Technology Integration Partner Program (TIPP), where any vendor's security stack integrates seamlessly with us. 。