IDS intrusion detection system
Identify spam events based on the user's security posture and frequency, and optimize the policy. Analyze and deal with threats with a de-technical wizard. Reduce the maintenance workload of users; It can correlate and analyze reported events, identify important alarms, and remind users to pay attention. It can accurately and efficiently detect common network threats, abnormal traffic, and other attack behaviors.
Product Overview:
With the rapid development of network technology, more and more organizations and individuals carry out organizational business and personal affairs through the network. The resulting information technology revolution has made the connection between people, organizations and organizations, and countries closer to countries: information sharing has become more convenient and information transmission has become more rapid. There is no doubt that the dependence of countries, organizations and individuals on the Internet is increasing, and the Internet has become an important pillar of the economic development of various countries, and it has also become an indispensable and important tool for organizations to conduct business and personal life. While network technology is developing rapidly, there are also many security issues and threats, such as network paralysis caused by large-scale worm outbreaks, economic losses caused by theft of bank accounts, data loss caused by virus infection, confidential leakage caused by illegal external links, business inability to operate normally due to large-scale botnet DDoS attacks, excessive use of P2P leads to exhaustion of network bandwidth, chats, videos, stock speculation, and games during work lead to reduced work efficiency, etc. The existence of these problems poses a threat to the business operation of organizations and the use of the network by individuals. So understand these threats: Where are the threats? What threats exist? How to eliminate threat mitigation risks? It has become a realistic task in front of us.
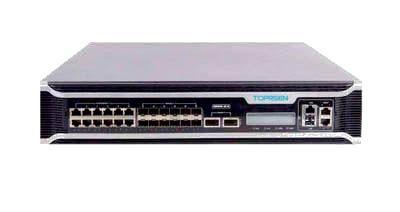
TOPRSEN® IDS intrusion detection and management system is the core technical team of SoftTrust and has completely independent intellectual property rights of threat detection, analysis and management products, which have high-precision detection capabilities for viruses, worms, Trojans, DDoS, scanning, SQL injection, XSS, buffer overflow, spoofing and hijacking and other attacks, as well as network resource abuse (such as P2P upload/download, online games, video/audio, online stock trading) and other threats, at the same time, The traffic module in this product has very accurate and effective detection capabilities for anomalies in network traffic. The product emphasizes the manageability of threats (such as threat analysis and threat handling) on the basis of accurate detection, especially the intelligent filtering of a large number of events that may occur, showing only the threats that really need attention to users, reducing the user's workload while ensuring the timeliness of threat handling.
Deployment and application
In different environments, the use of the TOPRSEN® IDS intrusion detection and management system can implement a variety of solutions. According to the needs of detection, it can be quickly and flexibly deployed in different locations such as network core, network boundary, and branch office. Moreover, different deployment and management schemes can be adopted according to the size of the enterprise.
For small networks: Due to its small scale and relatively flat structure, it is suitable for simple flat deployment and management solutions from the perspective of simplified management. In this environment, it is often only necessary to deploy a detection engine, adopt a single-level management mode, according to the needs of the management policy, you can choose to use the division of "virtual engine", and adopt sub-object virtualization management for the network (in the actual environment, virtualization management is very rare), generally speaking, in a small network environment, the use of "stand-alone engine + single-level management + single policy" is the most common situation.
For medium-sized networks: It is characterized by a relatively large organizational scale, a relatively complex network environment, and a relatively large number of hosts. In order to facilitate network threat management, the "partition monitoring + monitoring object division + multi-point deployment" scheme is usually used to cut threat management.
Partition monitoring: Different devices are used for monitoring different regional networks. Monitoring object division: Different hosts/network segments in the same area are divided into logical objects by virtualization (virtual engine), such as: the office network is divided into different departments according to network segments, and the production network is divided into different services according to different server addresses, etc., so that the monitored objects (servers, network segments) are mapped into assets, which is more conducive to threat management in medium-sized network environments. Multi-point deployment: Because of the partition monitoring, it is necessary to deploy multiple devices on multiple traffic aggregation nodes and adopt centralized management for threat management.
For large networks: It is characterized by large organizational scale, complex network environment, and a large number of hosts. For this kind of large network, in order to facilitate threat management, the node division solution is generally used to solve the problem. Specifically, "simple flattening or partition monitoring is adopted within the node according to the network size + the data flow is used from the bottom up between nodes, and the control flow is centralized management from the bottom down", and at the same time, according to the internal situation of each partition node, you can choose to use virtualization (virtual engine) to further map the monitoring area into assets. Hierarchical division: Mapping different branch nodes into independent management nodes at different levels for centralized management: Report the threat data of different branch nodes layer by layer according to hierarchical relationships, and centrally manage threats in the general control (root node). At the same time, the general control can also carry out maintenance work such as policy issuance, adding components, and system upgrades to the subordinate nodes as needed.